[DRAFT] Garbled Circuits: Commutative Encryption Protocol
Problem definition and a naive protocol
Definition
Alice has secret bits and Bob has secret bits . Alice and Bob are interested in computing an arbitrary boolean function so that at the end they both know the outcome, but neither of them learn anything more than the value of .
Relationship to Oblivious Transfer
Oblivious transfer (OT) refers to the case where Alice has a list of values , Bob wants to retrieve an element of without revealing to Alice. That is, at the end of the protocol Bob learns while Alice learns no information about and Bob learns nothing about the other elements in .
If we have this primitive, then to do two party computation Alice could compute a table , such that , for . Then Alice and Bob run OT on and so that at the end Bob learns the value , while revealing nothing about . Then he could share that value with Alice.
Note that the size of grows exponentially with making our above protocol impractical for large secrets.
Composing Oblivious Transfers
To avoid performing Oblivious Transfer on prohibitively large tables, we design a protocol for 2-party commutation so that the computation is done via a series of Oblivious Transfer like steps (one per gate). Each transfer only involves a table of constant size, and is done in a way that does not reveal the output of the gate. We present two ways to achieve that:
-
Public Encrypted Values: In this method, we stop the oblivious transfer at the point where the output value is encrypted with the keys of both Alice and Bob ( in the diagram above). For intermediate gates, we design protocols that are able to handle if one or both values are encrypted.
-
Shared Secrets: In this method, we make it so that for each intermediate value Alice knows and Bob knows so that . Oblivious Transfer is used to design gates that operate on pairs of secret values and produce a pair of secret values (so that only Alice knows , and only Bob knows ).
Composing Public Encrypted Values
As discussed in the previous section, when computing a single gate where a bit of the input is known by Alice, and another is known by Bob. Then Alice makes a table of the output of the gate depending on Bob’s value, and then Alice and Bob perform an oblivious lookup on the table to get the output of the gate. However, they stop at the step where the output is encrypted with both their keys. For the rest of this section we discuss how we can compute the output of intermediate gates where one or two of the inputs is encrypted.
Handling a single encrypted input
Motivation
Let’s say that we are interested in computing , where Alice knows , and is an intermediate value that’s encrypted in both Alice and Bob keys. It seems intuitive that we would want Alice to compute the output of this gate, since knowing it’s easier for her to compute the output in terms of ; for example, if , then . However, the issue is that if then . So unless the encryption has some special properties, computing the output might be challenging for Alice based solely of the encrypted value . To get around this, we give Alice access to three extra things. The encryption of which must be computed at the output of the previous gate. As well as valid encryption in Bob’s keys for , which they can share once at the beginning. This is motivated by the following lemma:
Lemma: For any binary gate , knowing , the output is always either , , or .
Proof. There are two cases:
- If , then we can use or .
- If , then we can use or .
Construction
-
At the beginning, each of Alice and Bob share valid encryption of and in their keys. (We are using IND-CPA secure encryption schemes.)
-
When running secret sharing in gates that only take as input values that are known to either Alice or Bob, we produce both , . (This can be done by replacing each entry in the table with a pair.)
-
When one of the inputs to the gate is a shared encrypted value (, for some ), and the other is known by Alice. Then Alice can compute the output purely from , , , . To prevent Bob from learning anything, Alice needs to re-randomize the encryption before producing the output. (This can be accomplished by decryption and re-encrypting with her key).
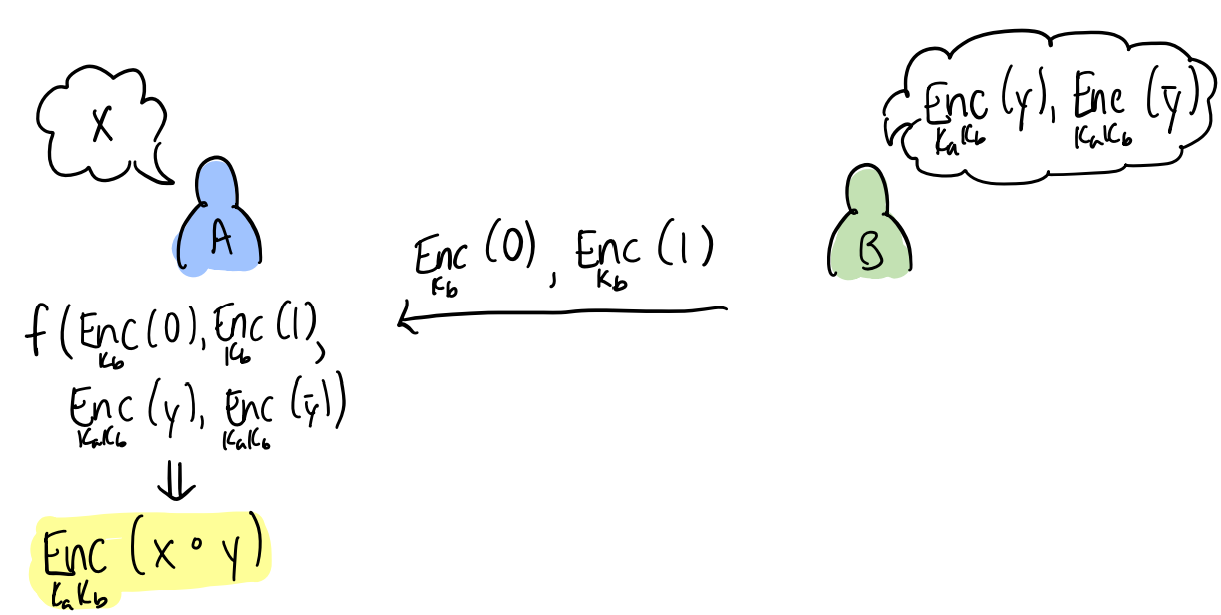
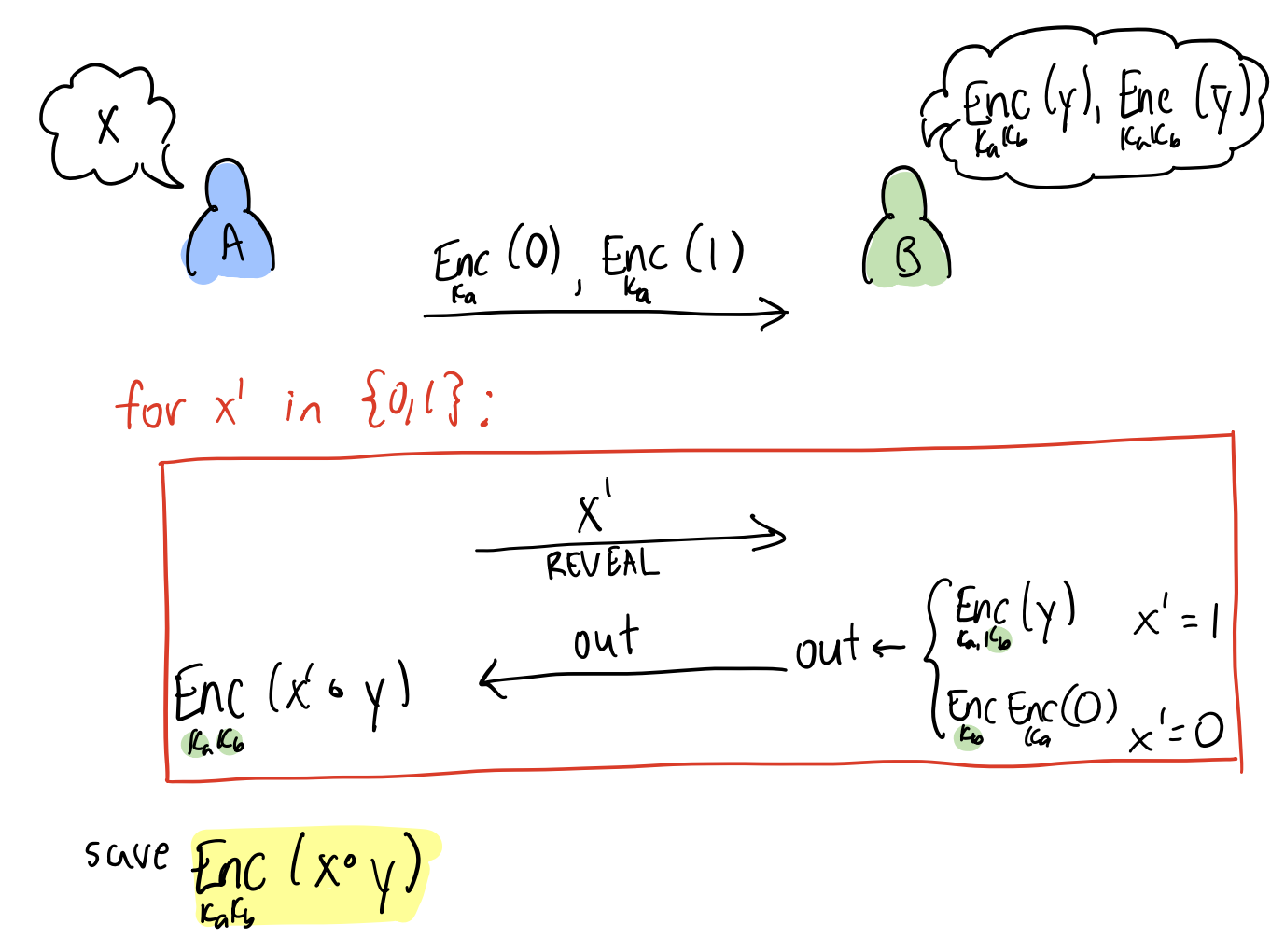
To motivate the next protocol, we can alternatively have Alice offload the work to Bob with the following protocol:
Handling two encrypted inputs
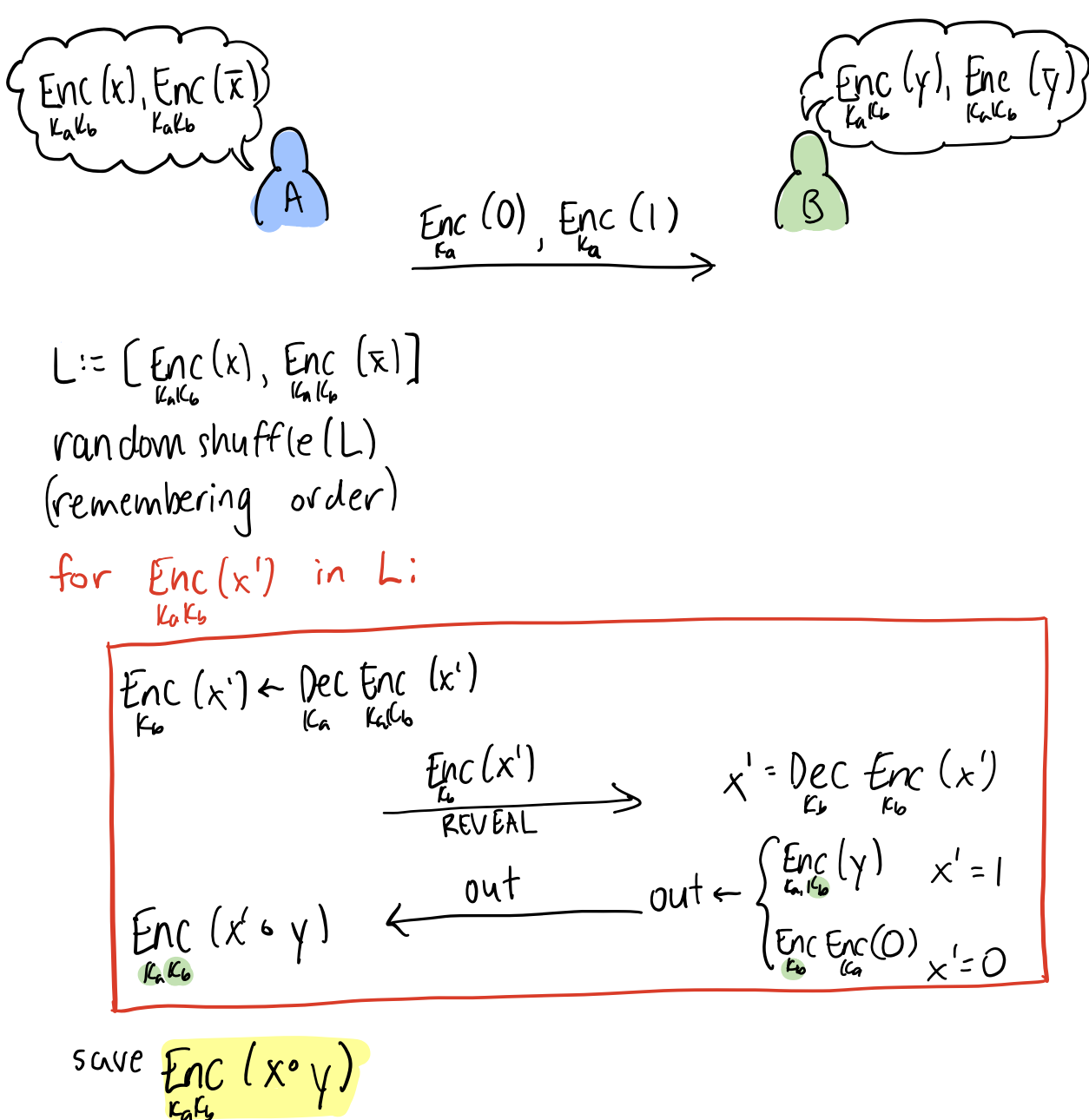
We reduce this case to the previous, by having one of the parties (Alice) reveal one of the secrets to the other (Bob). However, in order to prevent Bob from learning the value of the encrypted input , she reveals and to him in a random order. Bob computes the encrypted outputs , assuming both values; then Alice re-randomizes (by decryption and encrypting with her key). The re-randomization is crucial so that the Bob does not learn which of and is correct.
An example encryption function
There are many known commutative encryption schemes. See here for example. For completeness, we provide an example scheme that can work for our case. The downside for our simple method is that the size of the text grows linearly with the number of parties we want to be able to participate in the encryption.
The scheme depends on a cryptography sized group where discrete log is hard, and a known generator of the group.
- Setup: party computed a uniformly random number , and computes . is public, is not.
-
Encryption: The encryption of the message is a triple .
When a party (say party ) encrypts a plain text message , they generate and compute the first and last element of the tuple, the middle element is left as .
If party encrypts triple (where the first element is the identity), they similarly generate to compute first element, then they multiply the last element by . However, it’s important that they also randomize the coordinate associated with party (otherwise party might be able to identify the messages from their entry). To do they generate a random number , they multiply the middle element with , and the last element by
- Decryption: When party decrypts a message, . They produce the tuple: We see that if both parties decrypt the tuple, then , and the tuple is which allows them to read the message.
We leave it as exercise to the reader to see how this can extend to more than two parties by increasing the size of the tuple
Security Assumptions
Security against passive attacks
When using an IND-CPA secure encryption scheme, the protocol above does not reveal any information on the intermediate values (other than the final output). We can check this for each of our gate types:
-
Two known values: Security follows from the security of Oblivious Transfer.
-
One known values: Since the scheme is IND-CPA secure and the party who knows one of the values (Alice) re-randomizes the encryption, then other party (Bob) can not infer Alice’s bit because he can not distinguish the different message types (, , , ).
-
Zero known values: In this case, the random order of revealing and makes it so that Bob can not learn anything about until the point Alice picks the “correct” output. However, since Alice re-encrypts the output. Bob learns nothing by IND-CPA. Alice learns nothing from the safety of “one known value” gates.
The correctness of our scheme relies on the encryption being commutative.
An active attack
One kind of attack that’s possible in our scheme but not possible when we use oblivious transfer on the whole table of possible outputs is that Alice (or Bob) could give two different gates different values of . Depending on the structure of the circuit this might allow either Alice learn something it was not supposed to learn about Bob’s value (since this gives her control over more bits than the number of bits in her input).
Multiple parties
We leave it as an exercise to the reader to check that this scheme works for parties as follows:
-
When one of the input bits to the gate is known by at least some party, same scheme as above.
-
When both inputs are encrypted. One of the inputs (the pair ) is decrypted and randomly permuted by a sequence of of the parties, then the output is computed by the last party.
Note that the number of rounds per gate increases , though it is possible to get around by having the intermediate values encrypted by a subset of the parties (say ). (This decreases the rounds at the expense of making of the parties able to reveal intermediate values if they collude.)